Introduction:-
The strength of a nation’s currency is the foundation of its economic freedom and power. When that strength is damaged through the systematic injection of counterfeit money, the results go far beyond simple financial loss—they become a direct attack on the nation’s stability, security, and right to exist. This issue, called fake currency terrorism in this article, shows how asymmetric warfare has evolved in a dangerous way.
- Introduction:-
- Part I: The Weaponization of Value
- 1.1 What is Economic Terrorism and Fake Currency?
- 1.2 War by Other Means:-
- Part II: The Mechanics of Deception: Anatomy of Sovereign Currency Production
- 2.1 The “Substrate”: The First Line of Defense
- 2.2 Intaglio Printing:-
- 2.3 Advanced Optical and Magnetic Chemistry
- Part III: Historical Cases: Operation Bernhard and the Nazi Precedent
- Strategic Inception of Operation Bernhard
- The Sachsenhausen Production Line
- Strategic Pivot and Legacy
- Part IV: The North Korean “Supernote”: Government-Sponsored Crime
- Office 39: The Regime’s Secret Fund
- Anatomy of the Supernote
- Distribution Networks for Supernotes
- Part V: The South Asian Theater: Pakistan’s Strategic Asset in Fake Currency
- “Bleed India with a Thousand Cuts”
- The ISI-D-Company Nexus
- The Mechanics of Smuggling Routes
- i) The Malda Corridor (West Bengal)
- ii) The Nepal and Bangladesh Routes
- iii) The Dubai Hub
- Part VI: India’s Frontline: Impact, Policy, and Counter-Measures
- Economic and Security Impact of Counterfeit Currency
- The 2016 Demonetization: A Surgical Strike on Fake Currency
- Institutional Response: NIA and UAPA
- Recent Enforcement Successes (2024-2025)
- Part VII: Corporate Complicity and Global Scandals
- The De La Rue (United Kingdom)
- The “General G” Scandal: Oberthur Technologies in Bangladesh
- Crane Currency and the Liberian Inflation Crisis
- Part VIII: Middle Eastern Vectors: Proxies and Printing Presses
- Hezbollah and the Tri-Border Area
- Part IX: The Digital Frontier: Crypto-Terrorism
- From Paper to Blockchain: Digital Currency Threats
- The 2024-2025 Crackdown on Crypto-Terrorism
- Part X: Conclusion: The ‘Persistence of the Threat’
It is no longer just small criminal groups working in basements. Instead, it has grown into a large industrial operation backed by hostile governments, run by international crime syndicates, and helped sometimes knowingly and sometimes not by real companies in the global security printing business.
This article gives a complete analysis of the geopolitical, technical, and operational sides of fake currency terrorism. It follows the history from Nazi “Operation Bernhard” in World War II to modern “Supernotes” made by North Korea and the ongoing “bleed India” operation run by Pakistan’s Inter-Services Intelligence (ISI).
Part I: The Weaponization of Value
1.1 What is Economic Terrorism and Fake Currency?
Economic terrorism is the intentional damage to a nation’s economy by government or non-government actors to cause serious decline and political instability. Different from regular terrorism, which tries to kill people quickly to create fear, currency counterfeiting works over a longer, hidden timeline. Its purpose is to destroy the target nation’s ability to survive.
In the case of counterfeit currency, this economic warfare works through three main channels of causing harm:
Destabilization of Monetary Policy: The illegal injection of fake money disrupts central bank planning. If the amount of fake currency is large enough, it can artificially increase the money supply, leading to demand-pull inflation that makes the real currency worth less.
Erosion of Trust: Paper currency depends entirely on public trust. When citizens cannot tell the difference between real and fake notes, the speed of money movement slows, and people may look for other ways to store value (gold, foreign currency), triggering capital flight and economic instability.
Financing of Kinetic Terror: The cost of making a high-quality fake note is only a small part of what it’s worth. The “profit” made by the counterfeiter is effectively a theft of value from the target nation, which is then used to buy weapons, explosives, and recruit personnel for violent insurgency.
1.2 War by Other Means:-
Economic terrorism is the continuation of war through financial means. For countries like Pakistan or North Korea, fighting a direct traditional war with stronger enemies (India or the United States) is not militarily possible and would bankrupt them.
Fake currency offers a “sub-conventional” alternative. It is a low-cost, high-impact strategy that can be denied responsibility for while causing continuous damage to the enemy’s economy. The strategic logic follows an “encirclement” approach. By flooding a neighbor with counterfeit currency, a hostile nation can force the target nation to spend huge resources on internal security, border control, and constant currency replacement, effectively imposing a “security cost” on the target’s growth.
Part II: The Mechanics of Deception: Anatomy of Sovereign Currency Production
To understand the threat of fake currency terrorism, one must understand the technical barriers that counterfeiters must overcome. The making of “government-quality” fakes (such as the Supernote or high-quality FICN) requires access to the same industrial supply chains used by real governments.
2.1 The “Substrate”: The First Line of Defense
Real banknotes are not printed on “paper” in the traditional wood-pulp sense. They use a “substrate“, typically a blend of cotton and linen (rag paper), which gives the note its distinctive “crisp” feel and durability.
Security Features: The substrate is made with built-in security features that are part of the sheet itself, not printed on top. These include:
- Watermarks (made by changing paper density)
- Security threads (often magnetic or fluorescent)
- Embedded colored fibers for authentication
The Supply Chain Weak Point: The making of this security paper is controlled by a few European and North American companies. Investigations have shown that government-backed counterfeiters often break through security to get this specific paper, or they use their own government mills to copy the cotton-linen blend exactly.
2.2 Intaglio Printing:-
The main mark of genuine currency is intaglio printing. This process involves cutting the note’s design into steel plates. Ink is applied to the plates and then removed from the surface, leaving ink only in the cut grooves. Paper is then pressed onto the plate under huge pressure (up to 15,000 psi).
Tactile Result: This process pulls the ink out of the grooves and creates a raised texture on the paper that can be felt by running a finger over the portrait or number.
The Counterfeiting Challenge: Normal offset printing or digital inkjet printing (used by simple criminals) creates a flat image. To copy the raised feel of intaglio, a counterfeiter needs an industrial intaglio press, such as those made by KBA Giori (now Koenig & Bauer Banknote Solutions). These presses are strictly controlled and sold only to central banks and approved security printers.
2.3 Advanced Optical and Magnetic Chemistry
Modern notes use Optically Variable Ink (OVI), which changes color based on the angle of light (e.g., from green to copper). This effect is caused by the alignment of tiny crystal structures within the ink.
Magnetic Signatures: Machine-readable features, such as magnetic ink in serial numbers or threads, allow ATMs and counters to check notes. Counterfeiters in Pakistan have successfully copied these magnetic signatures, suggesting they have access to the specific chemical makeup of the inks used by the Reserve Bank of India.
Comparison: Genuine vs. Counterfeit Currency Features
| Feature | Genuine Note Method | Common Counterfeit Method | Government sponsored Counterfeit Method |
| Substrate | Cotton/Linen blend with embedded thread | Wood pulp paper, drawn thread | Real security paper obtained through corruption or government mills |
| Print Method | Intaglio (Raised Ink) | Offset/Inkjet (Flat) | Industrial Intaglio Press |
| Watermark | Changing paper density | Printed pale image | True cylinder-mould watermark |
| Ink | Optically Variable (Color Shift) | Metallic glitter or foil | Real OVI from legitimate suppliers |
Part III: Historical Cases: Operation Bernhard and the Nazi Precedent
The original example of modern government-backed currency terrorism is Operation Bernhard, conducted by Nazi Germany during World War II. It remains the largest counterfeiting operation in history and provides the historical foundation for understanding how currency is used as a weapon.
Strategic Inception of Operation Bernhard
In 1940, the Nazis created a plan to weaken the British economy by dropping millions of counterfeit pounds over the British Isles. The goal was to cause extreme inflation, making the Pound Sterling worthless and destroying the British war effort. The operation was first code-named Unternehmen Andreas (Operation Andreas) before being renamed Operation Bernhard under the leadership of SS Major Bernhard Krüger.
The Sachsenhausen Production Line
Krüger brought together a team of 142 Jewish prisoners at the Sachsenhausen concentration camp. These prisoners, picked for their skills in engraving, printing, and banking, were forced to work in Blocks 18 and 19, completely separated from the rest of the camp.
Technical Breakthroughs: The team discovered the British paper code (finding it was linen-based, not wood), copied the complex Britannia design, and figured out the pattern used by the Bank of England to make alphanumeric serial numbers.
By 1945, the unit had made approximately 8.9 million banknotes with a total face value of £134 million (some estimates go as high as £300 million). This represented a significant amount of the total real currency in circulation in the UK at the time.
Strategic Pivot and Legacy
The plan to drop the notes from planes was abandoned because the Luftwaffe no longer controlled the skies. Instead, the Nazis used the fake currency to pay for their own intelligence operations.
The Cicero Affair: The most famous use of this currency was the payment of £300,000 to Elyesa Bazna (code-named Cicero), the valet to the British ambassador in Turkey, in exchange for top-secret documents. Bazna later discovered his fortune was worthless.
Impact: The quality was so high that the Bank of England was forced to withdraw all notes higher than £5 from circulation after the war and completely redesign its currency. Operation Bernhard demonstrated that a sovereign nation, using its industrial resources for counterfeiting, could break the security of any paper currency.
Part IV: The North Korean “Supernote”: Government-Sponsored Crime
If Operation Bernhard was the historical foundation, North Korea’s “Supernote” is the modern perfection of fake currency terrorism. North Korea is the only government in the world known to make counterfeit currency of another sovereign nation—specifically the United States Dollar—as a matter of government policy.
Office 39: The Regime’s Secret Fund
The operation is managed by Office 39 (also known as Bureau 39 or Room 39), a secretive branch of the Workers’ Party of Korea created in the 1970s. Its job is to make hard foreign money for the personal use of the leadership (the Kim family) and to fund the country’s nuclear and missile programs.
Diversified Portfolio: Office 39 runs a worldwide network of illegal activities, including:
- Drug trafficking (methamphetamine)
- Insurance fraud
- Making of counterfeit goods (cigarettes, pharmaceuticals)
- Supernote production (the most daring product)
Anatomy of the Supernote
The “Supernote” refers to a counterfeit US $100 bill (and occasionally $50) that is of such high quality it can fool bank workers and standard detection machines.
Technical Equality: Investigations by US authorities showed that North Korea uses the same intaglio printing presses (obtained from Europe) and essentially the same ink and paper makeup as the US Bureau of Engraving and Printing. The notes contain:
- Correct red-and-blue fibers
- Security thread
- Watermark
- Color-shifting ink
Evolution: As the US updates its currency, Office 39 updates its fakes. When the US introduced the “big head” $100 bill and the color-shifting ink, the Supernotes followed suit shortly after.
Distribution Networks for Supernotes
North Korea uses its diplomatic immunity to distribute the currency worldwide.
The Diplomatic Pouch: North Korean diplomats have been caught in various countries carrying large quantities of Supernotes. The diplomatic pouch is immune to search, making it the perfect smuggling vessel for counterfeit currency.
Criminal Alliances: Office 39 has partnered with groups like the Official Irish Republican Army (OIRA). In a notable case, OIRA leader Sean Garland was indicted by the US for conspiring to distribute Supernotes in Europe. This alliance shows the connection between communist government actors and revolutionary terror groups.
Part V: The South Asian Theater: Pakistan’s Strategic Asset in Fake Currency
In South Asia, fake currency is not just a tool for making money; it is a core part of Pakistan’s military strategy against India. Indian intelligence agencies and worldwide reports consistently identify Pakistan as the production center for Fake Indian Currency Notes (FICN).
“Bleed India with a Thousand Cuts”
The Pakistani military approach, often attributed to General Zia-ul-Haq, aims to weaken India through proxy war, avoiding direct traditional conflict. FICN is a key weapon in this arsenal of economic warfare.
Dual Objectives:
Economic Sabotage: To make the Indian Rupee worth less and destabilize the banking system through systematic currency inflation.
Self-Financing Terror: To make the insurgency in Kashmir and terror operations in the Indian hinterland financially self-sustaining. The cost of printing a fake ₹1000 note is small (a few rupees), but it buys ₹1000 worth of explosives or loyalty in India.
The ISI-D-Company Nexus
The Inter-Services Intelligence (ISI) agency directs this operation, but the actual work depends on the criminal underworld.
Production Infrastructure: Intelligence shows that FICN is printed at the Pakistan Security Printing Corporation facilities in:
- Karachi
- Malir
- Peshawar
These facilities import security paper and ink from European suppliers, officially for Pakistani currency, but divert materials for FICN production.
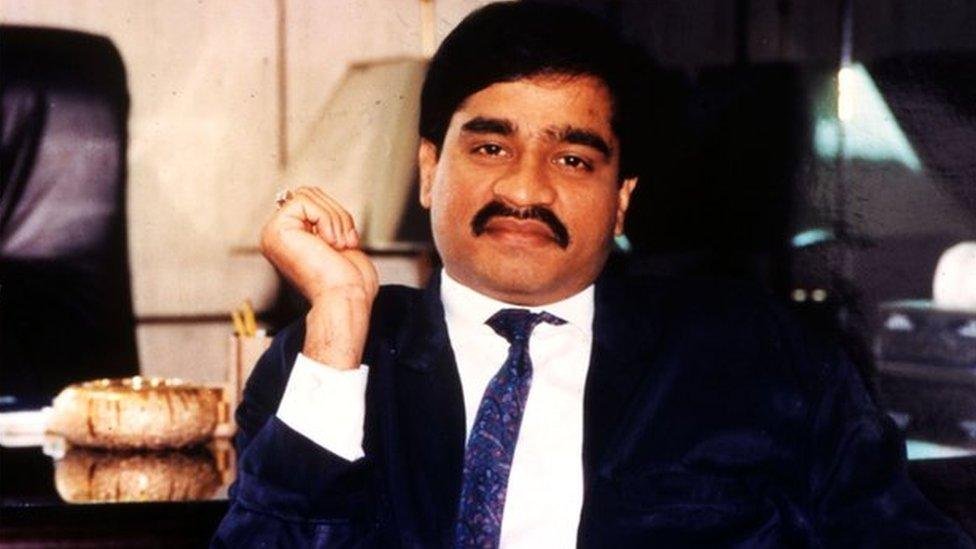
Logistics: The ISI uses the crime syndicate known as D-Company, led by the escapee don Dawood Ibrahim. Operating from Karachi, D-Company uses its established smuggling routes (originally built for gold and narcotics) to move fake Indian currency notes into India.
Key Operatives: Aftab Batki, identified as a key assistant of Dawood Ibrahim, manages the distribution network, ensuring the notes move from printing presses to couriers in Dubai, Nepal, and Bangladesh.
The Mechanics of Smuggling Routes
The “encirclement” of India is visible in the smuggling routes used for distributing counterfeit currency.
i) The Malda Corridor (West Bengal)
The district of Malda in West Bengal has become infamous as the “ground zero” of FICN entry into India.
Geography: The border here is riverine (the Ganges and its tributaries) and densely populated, making it hard to fence off.
Method of Operation: Smugglers use the “throw” method, tossing bundles of notes wrapped in plastic across the border fence or floating them across the river to counterparts on the Indian side. The Kaliachak block in Malda acts as a primary sorting and distribution hub from where couriers spread the notes via the Indian railway network.

ii) The Nepal and Bangladesh Routes
Nepal: Direct flights from Karachi to Kathmandu have been a traditional route. Couriers carry notes in luggage, taking advantage of the open India-Nepal border to cross into Bihar and Uttar Pradesh by road.
Bangladesh: Apart from Malda, other border points in Assam and Meghalaya are used. The cross-border movement is helped by local crime networks that operate on both sides of the divide.

iii) The Dubai Hub
Dubai serves as a financial clearinghouse for fake currency operations. FICN is flown from Pakistan to Dubai and then smuggled into India via air cargo or passengers, often mixed with real goods to avoid customs inspection.
Part VI: India’s Frontline: Impact, Policy, and Counter-Measures
The attack on the Indian Rupee has required a strong, multi-agency response from the Indian government to combat fake currency terrorism.
Economic and Security Impact of Counterfeit Currency
The circulation of FICN creates a “shadow economy” with serious consequences.
Terror Funding: The National Investigation Agency (NIA) has established direct links between FICN seizures and major terror attacks. For instance:
- The 2008 Mumbai attacks (26/11)
- The 2007 Hyderabad blasts
Both were partly funded through the proceeds of fake currency.
Inflation: While the total amount of fake notes might be small compared to the trillions in circulation, the concentration of these notes in high-denomination brackets (₹500 and ₹1000) maximizes their inflationary impact and loss of public confidence in the currency.
The 2016 Demonetization: A Surgical Strike on Fake Currency
On November 8, 2016, the Indian Modi government declared ₹500 and ₹1000 notes invalid.
Intent: One of the clearly stated goals was to “break the back” of the FICN networks. By making the existing stock of fakes worthless, the government aimed to destroy the accumulated terror finance money of the ISI and D-Company.
Outcome: The move successfully eliminated the stockpile of old fakes. However, it also sparked a competition. Within months, high-quality counterfeits of the new ₹2000 notes began appearing, showing the ability of the Pakistani printing presses to adapt quickly.
Institutional Response: NIA and UAPA
India has strengthened its legal and operational framework to combat economic terrorism and currency counterfeiting.
Legal Amendment: The Unlawful Activities (Prevention) Act (UAPA) was amended to classify the making, smuggling, or circulation of “High Quality Fake Indian Currency Notes” as a “Terrorist Act” (Section 15). This allows for stricter sentences and tougher bail conditions.
The TFFC Cell: The NIA created a specialized Terror Funding and Fake Currency (TFFC) Cell. This unit focuses exclusively on tracing the money trails of terror and counterfeit currency operations.
FCORD: The FICN Coordination Group (FCORD) was created by the Ministry of Home Affairs to ensure real-time intelligence sharing between:
- Border Security Force (BSF)
- Directorate of Revenue Intelligence (DRI)
- Central Bureau of Investigation (CBI)
- State police forces
Recent Enforcement Successes (2024-2025)
The increased focus on combating fake currency has produced significant results.
2025 Convictions: In January 2025, a Special NIA Court in Mumbai sentenced four individuals to five years of hard imprisonment in a FICN case involving the seizure of ₹13.67 lakh. The case highlighted the persistence of the Malda network, as one of the key accused, Sohrab Hosen, came from the region.
100% Conviction Rate: The NIA reported a 100% conviction rate in its cases for the year 2024, showing the effectiveness of its strategy in terror finance and fake currency cases.
Part VII: Corporate Complicity and Global Scandals
The infrastructure of fake currency terrorism is often helped by the corruption or failure of real European and American security printing companies. These companies supply the paper, ink, and technology that make “supernotes” possible.
The De La Rue (United Kingdom)
De La Rue is a giant in the currency printing world, but its history in India is backed by scandal involving counterfeit currency threats.
The Breach: In 2010-2011, the Indian government blacklisted De La Rue after it was found that the company had supplied poor-quality paper. More seriously, intelligence reports suggested that the specific security features (such as the security thread specifications) of Indian notes had been compromised and shared with Pakistan.
Implication: This breach allowed Pakistani presses to print FICN that was impossible to distinguish from genuine notes, as they were using the exact same paper and security threads. The scandal showed the danger of outsourcing sovereign currency making.

The “General G” Scandal: Oberthur Technologies in Bangladesh
A telling case of corruption in the security printing sector involved the French company Oberthur Technologies (now IDEMIA) and the Bangladeshi National Identity (NID) card project.
The Scheme: To secure a contract for NID cards, Oberthur paid approximately €6.1 million in bribes to a Bangladeshi official codenamed “General G.” Investigations identified “General G” as Major General Tarique Ahmed Siddique, the security advisor to the then-Prime Minister Sheikh Hasina.
The Mechanism: Bribes were sent through:
- Tiger IT (a Bangladeshi subcontractor led by Ziaur Rahman)
- Decatur Europe (a UK-based supplier)
The payments were hidden as “training fees” and “consultancy” contracts.

Source: wikipedia (General Tarique Ahmed Siddique)
Consequences: The World Bank banned Oberthur and Tiger IT for corrupt practices. While this case involved ID cards, it shows how high-ranking defense officials and security printing companies work together, creating weaknesses that hostile actors can use for identity fraud and counterfeiting.
Crane Currency and the Liberian Inflation Crisis
Crane Currency, a US-Swedish company, was involved in a destabilization scandal in Liberia.
The Incident: An investigation by the Liberian legislature found that Crane Currency had printed L$10 billion in excess banknotes that were not approved by the legislature. This huge injection of unauthorized money led to severe inflation and economic trouble in Liberia.
Significance: This case shows how a company, operating with weak central bank oversight, can effectively act as an economic saboteur, flooding a country with excess money and causing currency terrorism effects.
Table 1: Major Corporate Scandals in the Security Printing Industry
| Company | Country Origin | Scandal | Impact |
| Da La Rue | United Kingdom | Supplied compromised security paper to India; allegedly leaked specs to Pakistan (2010). | Enabled making of high-quality FICN by ISI; led to ban in India. |
| Oberthur technologies | France | Paid €6.1m bribes to “General G” (Maj. Gen. Tarique Siddique) in Bangladesh for ID contracts | Compromised integrity of national identity infrastructure; World Bank ban |
| Crane currency | Sweden, USA | Printed unauthorized L$10 billion excess banknotes for Liberia. | Caused massive inflation and economic instability in Liberia. |
| Rayan printing | Iran | Printed counterfeit Yemeni Rials for IRGC-Qods Force. | Funded Hezbollah/Houthis; destabilized Yemeni currency. |
Part VIII: Middle Eastern Vectors: Proxies and Printing Presses
The Middle East presents a complex area where fake currency is used by government sponsors (Iran, Russia) to fund proxy militias (Hezbollah, Houthis, Haftar).
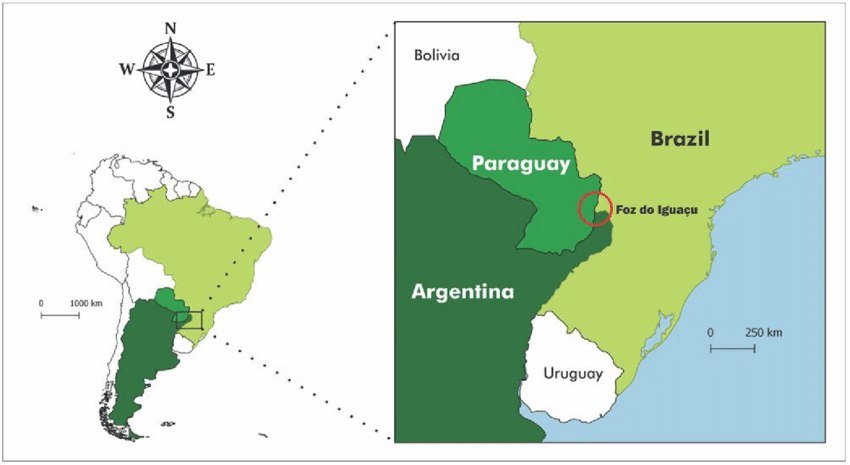
Hezbollah and the Tri-Border Area
The Tri-Border Area (TBA) where Argentina, Brazil, and Paraguay meet is a lawless zone known as a hub for terror financing and currency terrorism.
Convergence: Hezbollah uses the TBA to clean money through the trade of counterfeit goods (electronics, cigarettes) and currency. The Barakat Clan, a major Hezbollah financial network, operates extensively here.
The Rayan Printing Connection: In a direct link to government backing, the US Treasury designated the Iran-based Rayan Printing company for making counterfeit Yemeni rials worth hundreds of millions of dollars for the IRGC-Qods Force. These funds were used to help Hezbollah and other Iranian proxies, destabilizing the region’s economy while avoiding financial sanctions.
Part IX: The Digital Frontier: Crypto-Terrorism
As physical borders harden and currency security features become more complex, the location of “fake value” is moving to the digital world. While not “counterfeit” in the physical sense, the creation of illegal value through cryptocurrency fraud and theft represents the next evolution of fake currency terrorism.
From Paper to Blockchain: Digital Currency Threats
Terror groups like ISIS and Hamas have aggressively adopted cryptocurrency to bypass the banking system.
The Mechanism: Instead of printing fake notes, these groups use:
- Phishing attacks
- Hacking and theft
- “Fake” transaction schemes (e.g., selling non-existent PPE during COVID-19 via sites like FaceMaskCenter.com)
Fake Value: They also use “wash trading” and market manipulation to increase the value of crypto assets before cashing out, effectively creating value out of thin air to fund operations and conduct economic terrorism.
The 2024-2025 Crackdown on Crypto-Terrorism
Recent years have seen major enforcement actions against these digital networks and currency terrorism actors.
Seizures: In 2024 and 2025, US and Israeli authorities executed major seizures of cryptocurrency wallets linked to Hamas and ISIS. These operations stopped millions of dollars in:
- Tether (USDT)
- Bitcoin
These assets were intended for terror logistics and operations.
The TRON Network: Reports show that terror financiers have moved toward the TRON blockchain because of its lower transaction fees and speed, prompting the creation of the T3 Financial Crime Unit to fight illegal activity on that specific chain.
Part X: Conclusion: The ‘Persistence of the Threat’
Fake currency terrorism is a tough and changing threat. It takes advantage of the fundamental trust that societies place in their medium of exchange. From the concentration camps of Nazi Germany to the high-security printing presses of Karachi and the dark web crypto-wallets of ISIS, the objective remains the same: to use value as a weapon against the nation.
For India, the threat is crucial and ongoing. The “bleed India” approach of Pakistan continues to rely on FICN as a low-cost, high-impact weapon. The complicity of worldwide companies like De La Rue and Oberthur highlights that this is not just a regional security issue but a failure of worldwide corporate governance.
The weaknesses in the supply chain of security paper and ink allow hostile nations to get around the technological barriers built by central banks. As the world moves toward digital money, the threat will not go away it will move to digital. The “Supernote” of the future may not be a $100 bill, but a counterfeit digital token or a compromised central bank digital currency (CBDC).




